
How do your production assets stay cyber-secure?
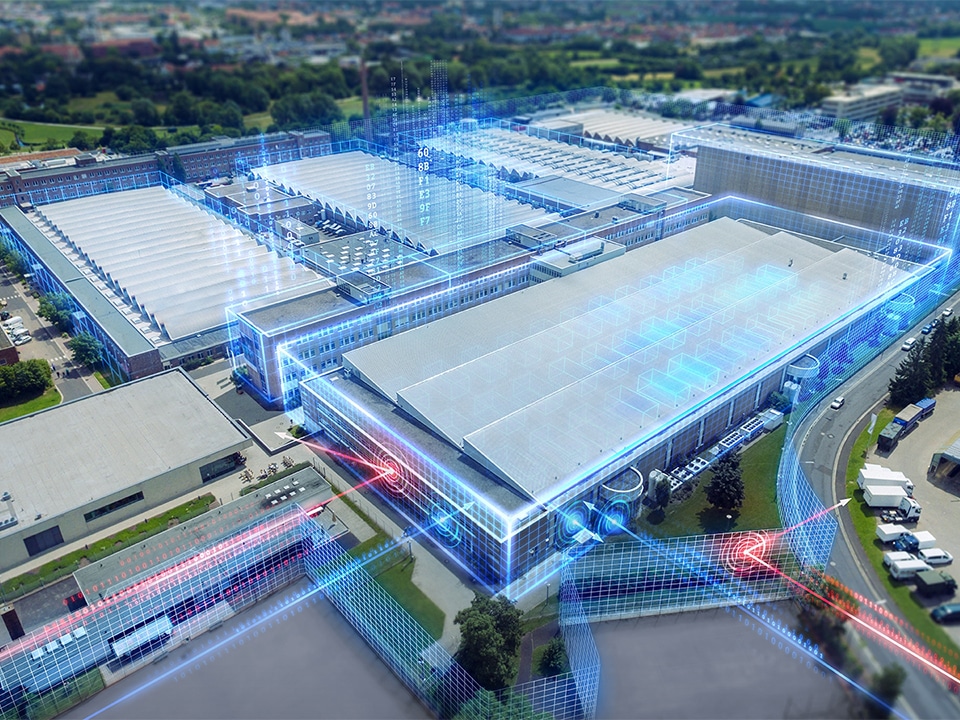
The worlds of IT and OT may be increasingly converging, but in terms of security, you would do well to keep two separate networks. To help you set up a secure yet workable topology from shopfloor to topfloor and back, turn to the products and services of Siemens. A specialised team can help lay out the roadmap to cyber security for any company and any budget.
A study by consultancy BDO published in January found that hackers can easily penetrate almost one in five company and government websites. But this is just the tip of the iceberg. Because there are also real dangers for manufacturing. Geert De Coninck, Business Unit Manager Factory Automation: “Companies” awareness of cyber security has fortunately increased considerably in recent years. The fact that more and more incidents reach the press has a lot to do with that. They are aware of the danger, yet it is no easy task to find a conclusive solution, because the world of IT and OT networks is just as different. The person in charge of the production floor looks to the IT manager to plug security holes and vice versa. New profiles such as Chief Information Security Officers, who have to monitor the cyber security of all assets, show that things are changing."

Geert De Coninck: “It is important to build a bridge between IT and OT and see cyber security as a holistic approach.” 
Johan Van den Eede: “A network in production, where flexibility and uptime are key, has completely different requirements and response times than an office network.”
Segmentation crucial
But how do you make your company cyber-secure, because a digital factory also cannot do without a powerful communication network? “Everything starts with a good segmentation,” opens Johan Van den Eede, Industrial Networks sales specialist. “A network in production, where flexibility and uptime are the watchwords, has completely different requirements and response times than an office network that is all about transparency. The fact that there is a separate certification around it, IEC 62443 (for industry) and ISO 27000 (already known in IT) respectively, makes it clear that although the challenges are the same, the solutions are different.” So two networks, which remain separated by a so-called demilitarised zone, but where a powerful firewall such as Palo Alto Networks NGFW does provide a secure bridge between the two worlds.
That is not the end of the matter as far as segmentation is concerned. Van den Eede: “With the SCALANCE S switches, the production floor can also be further divided into cells, which are then given a ring topology. This can keep the swapping time below 300 ms. A simple firewall between the different cells or even per cell (depending on cyberrisk versus impact) then suffices to keep everything wall-tight.”
Building cyber security step by step
Invest in a central monitoring and management system such as SINEC NMS is an interesting next option. “It's all about knowing what's running on a network. Configuration management, fault management, performance, security ... all assets, including peripherals are monitored immediately,” Van den Eede points out. Tools from the IT world do not have that same robustness and features needed in an industrial environment. A network management system such as SINEC NMS will also be able to perform typical Profinet diagnostics.” Those who want to work in compliance with standards will also need a central user and access management system. This makes it clear which profiles are allowed to perform which tasks on which part of the network. It is also important to implement patches and backups in a structured way. “For users, it is not obvious to know the consequences of applying such a patch. A team from Siemens therefore advises which patches can be done and when an alternative is more interesting.” Finally, to completely secure a network, it is a good idea to test the assets for vulnerability. Van den Eede: “Siemens has already done that itself for 63,000 components. You can use SINEC NMS to check which patches and firmware your assets need. Other things one can still add to security are anomaly detection and system hardening, more advanced techniques.”

No hacks without human error
Exactly what security is needed will differ in each company. “Cyber security should always start from an assessment,” De Coninck points out. “On the one hand, to know how attractive your company is as a target for hackers. On the other, to identify the crown jewels - those machines or installations where you cannot afford downtime - in the production process itself. That's where security may be raised a bit anyway.” As much as technology can help ‘plug’ gaps in security, the ‘human’ factor is still crucial in this story. “Cyber security is and always will be a balancing act between creating as secure and as workable as possible. Make sure everyone on staff is imbued with the proper, secure way to handle assets. Most hacks happen through carelessness. That is also why it is so important to build a bridge between IT and OT and see cyber security as a holistic approach,” De Coninck concludes.





